How to Bypass CAPTCHA in 2026 (The Guide That Doesn't Waste Your Time)

"Check the top 20 results for 'best running shoes' on Google and pull the prices."
Your AI agent opens a browser, navigates to Google, and hits:
"Our systems have detected unusual traffic from your computer network. Please try again later."
Not even a CAPTCHA puzzle. Just a wall. Your agent can't solve it, can't retry its way past it, and now you're manually pulling data from Google search like it's 2005.
This is the 2026 CAPTCHA experience, and most tutorials on "how to bypass CAPTCHA" are still teaching 2020 tricks. They don't work anymore. This piece covers what actually does — and where each approach fails — so you stop burning hours on stealth configs that Cloudflare patched six months ago.
- 1"How to bypass CAPTCHA" in 2026 is mostly "how to not trigger a CAPTCHA" — because modern systems score your browser before any puzzle appears.
- 2CAPTCHA-solving services (2Captcha, CapSolver) still work on legacy image CAPTCHAs but fail on reCAPTCHA v3, Cloudflare Turnstile, and DataDome.
- 3Stealth plugins for Playwright and Puppeteer are a maintenance treadmill; every detection update breaks them, usually for days at a time.
- 4Residential proxies fix the IP signal but not the browser fingerprint signal — necessary but not sufficient.
- 5Real-browser takeover passes all four major anti-bot systems because the browser actually is real, with real history and real cookies.
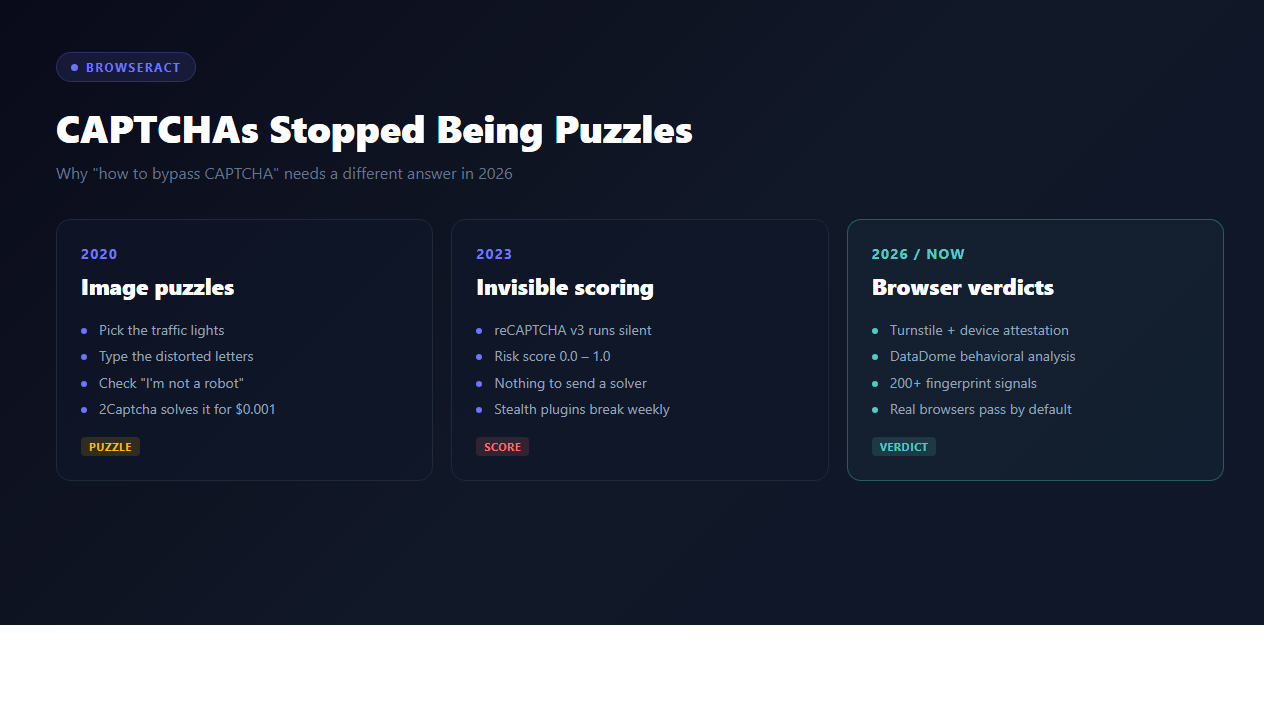
What "Bypass CAPTCHA" Actually Means in 2026
Three very different things all get called "bypassing CAPTCHA":
1. Solving the visible challenge — click the right images, type the right letters, let a service answer the puzzle
2. Avoiding the challenge — make the browser look normal enough that the site never shows a CAPTCHA in the first place
3. Proxying past the challenge — use a pre-authenticated session where the CAPTCHA already passed
In 2020, #1 was the whole game. Send the puzzle to 2Captcha for $0.003, get the answer back, paste it in, done.
In 2026, #1 barely works. The big CAPTCHAs stopped being puzzles. reCAPTCHA v3 runs silently in the background and assigns a risk score between 0.0 and 1.0 — there's no puzzle to send anywhere. Cloudflare Turnstile does the same thing but with device attestation. DataDome doesn't even show CAPTCHAs most of the time; it just returns empty pages or fake data to browsers it doesn't trust.
So "how to bypass CAPTCHA" has quietly become "how to not trigger a CAPTCHA in the first place." The industry shifted. Most guides didn't.
The 5 Approaches (And Where They Actually Work)
Approach 1: CAPTCHA-Solving Services (2Captcha, Anti-Captcha, CapSolver)
How it works: You hit a CAPTCHA page, your code ships the challenge to the service's API, a human (or ML model) in a low-wage labor market solves it, you get the answer, you submit it.
Pricing in 2026:
- reCAPTCHA v2: ~$1 per 1,000 solves
- hCaptcha: ~$1.50 per 1,000
- reCAPTCHA v3 (token): ~$2 per 1,000
- Cloudflare Turnstile: most services list it but success rates are low (~40%)
- DataDome: most services don't offer it at all
When it works: Legacy forms, older sign-up pages, government portals, CMS login pages that still use image-grid reCAPTCHA v2. If the target shows an actual puzzle and accepts a static token, these services still do the job for pennies.
When it doesn't: Any modern site. The moment the check becomes behavioral ("did this browser scroll like a human in the last 10 seconds?"), there's no puzzle to send to 2Captcha, because the puzzle never renders — the site just quietly decides you're a bot and moves on.
Verdict: Still useful, still cheap, but the target surface is shrinking fast.
Approach 2: Stealth Plugins (playwright-extra, puppeteer-stealth, undetected-chromedriver)
How it works: Patch your headless browser to hide obvious automation signals — spoof navigator.webdriver, fake a plugin list, inject realistic canvas noise, match a known Chrome version's TLS fingerprint.
Pricing: Free (open-source).
When it works: Sites running basic bot detection that checks shallow signals. If the target's only question is "is navigator.webdriver true?", a stealth plugin answers "no" and you're through.
When it doesn't: Modern stacks check 200+ signals across TLS handshakes, WebGL rendering, audio context, font lists, behavioral timing, and session history. Every time Cloudflare or DataDome adds a new signal, the open-source stealth community has to catch up. The gap is usually weeks. In that gap, you're blocked.
From r/webscraping: "Stealth worked for two weeks. Then Cloudflare updated something and my whole pipeline died overnight. Spent three days debugging before I realized it was a detection update, not my code."
Verdict: The treadmill is real. You'll maintain the stealth config forever, and you'll still lose every time there's a detection update. Viable only if scraping is your full-time job.
Approach 3: Residential Proxies + Rotating IPs (Bright Data, Oxylabs, IPRoyal)
How it works: Instead of scraping from a datacenter IP (which every anti-bot vendor has blacklisted), route your requests through residential IPs — real home internet connections rented out through proxy networks.
Pricing in 2026:
- Bright Data residential: ~$15 per GB
- Oxylabs residential: ~$10 per GB
- IPRoyal residential: ~$6 per GB
- Mobile IPs (highest trust): $20-40 per GB
When it works: IP reputation is a huge component of the risk score. A clean residential IP can take a marginal stealth config from 40% success to 80%+.
When it doesn't: IP is just one signal of many. A perfect residential IP paired with a headless Chrome that has a freshly-generated fingerprint still gets scored as suspicious. Proxies don't fix browser-level detection.
Verdict: Necessary but not sufficient. Add to your stack if you're already running stealth plugins, but don't expect it to be the one-shot fix.
Approach 4: Pre-Authenticated Session Reuse
How it works: Login manually in your real browser once, export the cookies, inject them into your automation tool. The session is already trusted; no CAPTCHA fires because the site sees you as a returning user.
When it works: Sites that use session-based trust. Once you're logged in, most anti-bot systems relax the scrutiny — you're a verified user, not an anonymous visitor.
When it doesn't:
- Sites that re-run CAPTCHA checks on sensitive actions (transfers, signups, bulk actions)
- Sessions that expire (most do, within hours to days)
- Sites that check device fingerprint continuity — if the cookie was set in your Chrome but now a headless Chrome is using it, that's a red flag
Verdict: Works great for personal automation. Doesn't scale.
Approach 5: Real-Browser Takeover
How it works: Your automation runs inside a real browser you already use — the one with your daily session cookies, normal fingerprint, and months of browsing history. The anti-bot systems see a real browser because it is a real browser.
When it works: Everywhere modern CAPTCHA systems operate. Cloudflare Turnstile, reCAPTCHA v3, DataDome, PerimeterX — all of them score your session as trusted when the browser passes real-world signals.
When it doesn't:
- High-stakes sites that explicitly re-challenge even known users (some banks, some Google admin tools)
- When you need to scale to thousands of parallel sessions from a single machine
Verdict: This is where the 2026 scrapers are moving. Not because it's sexy — because it's the only approach whose success rate goes up as anti-bot systems get more sophisticated, not down.
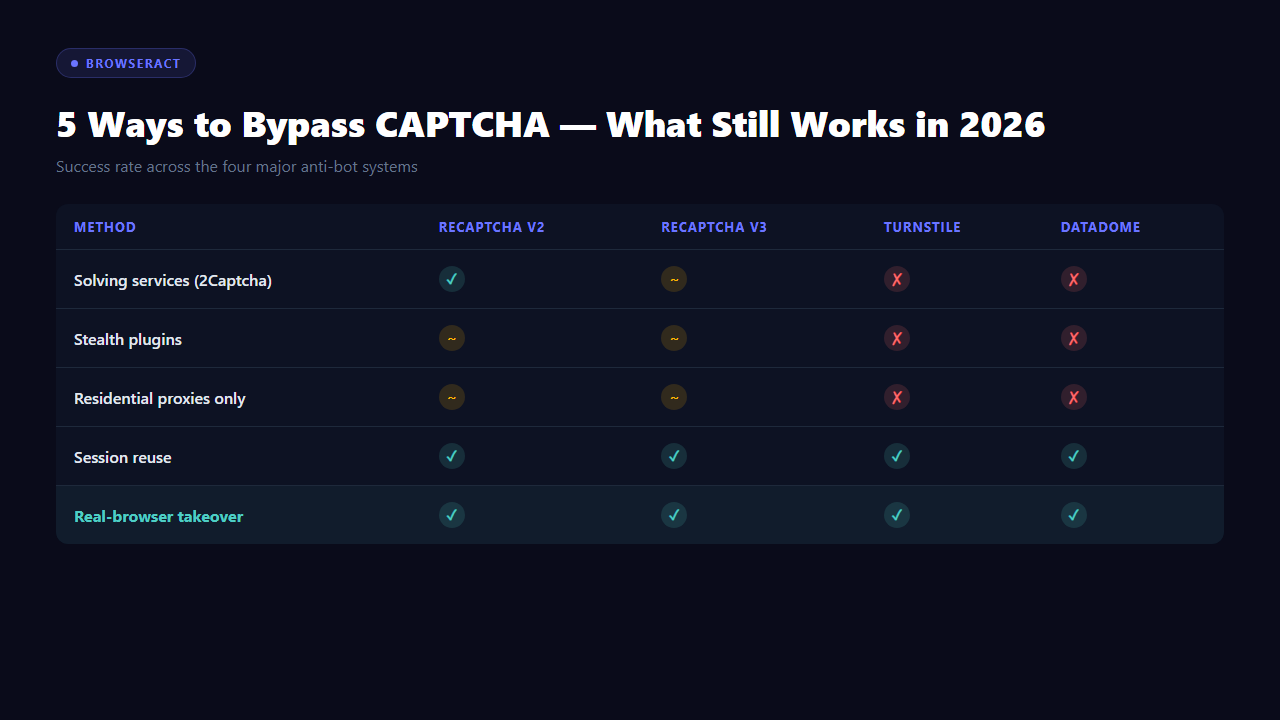
Comparison: What Passes What in 2026
Approach | reCAPTCHA v2 | reCAPTCHA v3 | Turnstile | DataDome | Monthly Cost | Maintenance |
Solving services | ✅ ~95% | ⚠️ ~60% | ❌ ~30% | ❌ ~10% | $1–$3 / 1,000 | Low |
Stealth plugins | ⚠️ Variable | ⚠️ Variable | ❌ Usually blocked | ❌ Usually blocked | Free | Very high |
Residential proxies alone | ⚠️ Marginal | ⚠️ Marginal | ❌ Blocked | ❌ Blocked | $6–$20 / GB | Low |
Session reuse | ✅ Good | ✅ Good | ✅ Good | ✅ Good | Free | Medium (expiry) |
Real-browser takeover | ✅ Rarely fires | ✅ Rarely fires | ✅ Rarely fires | ✅ Rarely fires | Free (local) | Very low |
The numbers aren't subtle. The approaches that worked in 2020 barely clear the modern stack; the one that works in 2026 isn't trying to defeat CAPTCHAs at all.
Stop getting blocked. Start getting data.
- ✓ Stealth browser fingerprints — bypass Cloudflare, DataDome, PerimeterX
- ✓ Automatic CAPTCHA solving — reCAPTCHA, hCaptcha, Turnstile
- ✓ Residential proxies from 195+ countries
- ✓ 5,000+ pre-built Skills on ClawHub
What Actually Works: Use a Real Browser
If you've been fighting CAPTCHAs for more than a week, the move isn't "a better stealth plugin." It's to stop pretending your headless Chrome is a real browser and just use a real one.
Tools like BrowserAct make this direct: they hand control of your Chrome — the one you use daily, with your real fingerprint and session cookies — to an AI agent. For Cloudflare, the agent looks identical to you, because technically it is you.
For the specific workflows where CAPTCHAs used to be the daily blocker — price monitoring, lead generation, competitor research, Reddit scraping — the Amazon Product Search API, the Google Maps API, and the Reddit Posts & Comments Scraper template handle the whole pipeline through real browser sessions the target sites already trust. CAPTCHAs don't fire, not because they got bypassed, but because they never got triggered.
The uncomfortable truth: most of the "how to bypass CAPTCHA" content on the internet is teaching you to fight a war the defenders already won. The open door is next to it.
When Traditional Bypass Still Makes Sense
This guide has been rough on legacy approaches, but they're still the right tool sometimes:
- Legacy reCAPTCHA v2 forms: 2Captcha is $0.001 per solve. Don't overthink it.
- One-off manual tasks: If you hit a CAPTCHA five times a month, a browser extension like Buster is fine.
- Accessibility tooling: Buster's audio-to-text approach is the same thing blind users rely on.
- Proof-of-concept demos: Stealth + proxy works well enough for a demo video. Just don't run it in production.
The mistake is scaling a legacy approach. At scale, every solve costs money, every new detection signal breaks your stealth config, and every Cloudflare update burns a weekend. The math stops making sense past a few thousand requests a day.
Conclusion
The honest answer to "how to bypass CAPTCHA in 2026" is that the question needs to be rephrased. The tools that defeat puzzles are solving a problem that barely exists anymore. The tools that avoid puzzles — by running automation inside a real, trusted browser — are solving the problem that actually shows up in production.
For anyone tired of waking up to broken scrapers and stealth configs that worked last Tuesday: BrowserAct is the shortest path out of the treadmill. Local-browser mode is free, and CAPTCHAs stop firing because the browser was never suspicious in the first place.
The CAPTCHA isn't the wall. The fake browser is.
Automate Any Website with BrowserAct Skills
Pre-built automation patterns for the sites your agent needs most. Install in one click.
Frequently Asked Questions
Can CAPTCHAs still be bypassed in 2026?
Yes, but mostly by not triggering them in the first place. Traditional solvers still handle legacy puzzles but fail on Turnstile, reCAPTCHA v3, and DataDome.
What's the cheapest way to bypass CAPTCHA?
For legacy reCAPTCHA v2, 2Captcha at ~$1 per 1,000 solves. For modern systems, real-browser takeover (free in local mode) is both cheapest and most reliable.
Is it legal to bypass CAPTCHA?
Bypassing CAPTCHA on sites you own or have permission to automate is legal. Doing it to violate a site's terms of service or access restricted data typically is not.
Does ChatGPT or Claude solve CAPTCHAs?
No — both explicitly refuse. They also can't access the web in real time for most tasks. CAPTCHA-handling requires a browser-level tool, not a chat model.
What's the best CAPTCHA solver in 2026?
Depends on the CAPTCHA. 2Captcha for legacy image puzzles, Buster for audio challenges, real-browser automation for everything modern (Turnstile, reCAPTCHA v3, DataDome).
Why does my scraper work for a few days then stop?
You're almost certainly relying on a stealth plugin whose fingerprint got detected. Anti-bot systems update detection signatures continuously; open-source stealth lags behind.
Can residential proxies alone bypass CAPTCHAs?
No. They fix the IP reputation signal but not browser fingerprint, TLS fingerprint, or behavioral signals. Necessary for scale, not sufficient on their own.
Relative Resources

Using AI Browser Automation for Software Testing and Frontend Debugging

Chrome DevTools MCP Invalid URL Error: How to Fix Initialize Failures

AI Computer Use Security: How to Sandbox Agents Before They Touch Your Browser and Files

AI Browser Automation Login Problems: Google Auth, 2FA, and Manual Takeover
Latest Resources

Remote Assist for Browser Automation: Human Handoff Without Breaking the Agent

Headless Browser Automation With Human Takeover

From Browser Scripts to AI Operators: Why Teams Need Auditable Browser Workflows

